Cloud security refers to a broad set of policies, technologies and controls employ to protect data applications and the associated infrastructure of cloud computing. It gives protection of data stored online from theft, leakage, and deletion. Cloud security include firewalls, penetration testing, virtual private networks (VPN) and avoiding public internet connections. The threat to cloud security include data breaches, data loss, account hijacking, service traffic hijacking, insecure application program interfaces (APIs), poor choice of cloud storage providers and shared technology that can compromise cloud security.
A secured system is a reliable system. Cloud native applications are secured applications. In many cases, cloud providers will have stronger security than any individual company can maintain and manage on premise.
- To make it easier and faster for you to meet security compliance requirement we provide compliance reports based on managing thousands of security controls inherited through the AWS platform.
- Our security solutions help to avoid data breach issues, with strong data encryption. It ensures that the multi-tenant cloud service database is properly designed and configured to keep hackers away from the system.
- It help to recover lost data. Regular updated offline data backups reduce risks of data loss.
- Our service helps users to identify and improve weak APIs that can expose the organization. More secure API.
- Reduction of malicious threats.
- Our cloud computer service provides a solid solution to prevent former employees, contractors and business partners from gaining access to a cloud network.
- Web Application Security
- Vulnerability Assessments
- Real Time Log Flow Analysis
- Log Manager
- Network Intrusion Detection And Prevention
- Consulting On Your Cloud Strategy

We provide security operations that enable you to tailor the level of security to your budget, risk and compliance needs. We integrate cloud security concerns into your overall cyber security architecture, which reduces risk from unauthorized cloud services.
Our Extensive Accomplishment
Explore Our Versatile Portfolio: Software, Logistics, Mobile & Web Solutions
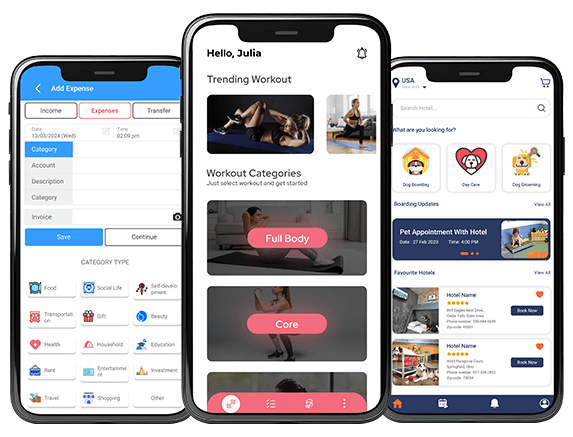
Delve into our comprehensive portfolio, a testament to our prowess across various domains, including software development, logistics solutions, mobile app development, and web development. With a keen focus on optimizing supply chains and enhancing operational efficiencies, we consistently deliver solutions that epitomize excellence and innovation.
Explore the breadth and depth of our portfolio to witness firsthand how we blend technical expertise with creative ingenuity to drive tangible results and propel our clients towards success.
Your inquiry is precious to us. We will be delighted to help you in your queries. Our customer care representative will be back to you shortly within 24 hours and would be delighted to do free analysis of your requirement. For prompt reply please contact us on Phone No: +91 87 80064339. Otherwise we will revert back to you on your email. Until then make certain to have a look at our resources blog, portfolio, products